Mount Locker ransomware takes a double extortion route
Another ransomware campaign called Mount Locker is focused on retrieving victims’ data before malicious encryption and then expecting huge ransoms.
Mount Locker, a relatively new name in the ransomware arena, debuted in July 2020 with assaults targeting enterprise networks. Judging by ransom notes observed by security analysts who have looked into these early attack incidents, the crooks demand millions of dollars’ worth of Bitcoin for data decryption.
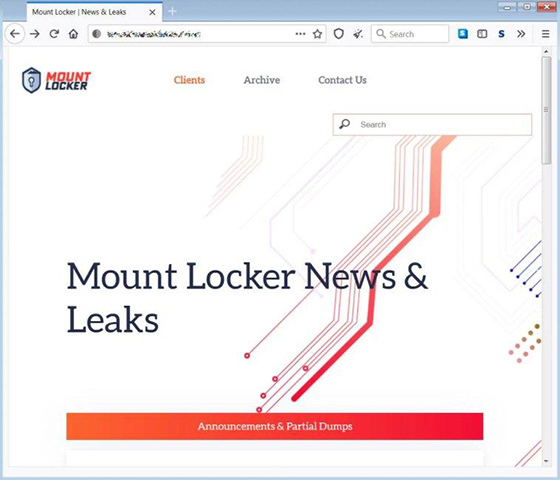
The ransomware operators pilfer their victims’ important files before locking them down. This access is used as extra leverage that’s supposed to pressure stubborn companies into paying up – if they don’t, crooks threaten to post the information on the Mount Locker leak site shown below.
According to researchers’ findings, the attackers contacted one of the victims and claimed to have obtained 400 GB of proprietary records. The message contained an ultimatum: if a ransom is not paid, the felons will spread the word about the attack via the media and disclose the stolen files to the company’s competitors.
This particular business chose not to follow the demands, only to discover shortly that their data was uploaded to the above-mentioned leak site. At the time of this writing, the site mentions four victims, but only records belonging to one of them have been published so far.
Inner workings of the Mount Locker ransomware
Malware analysts hadn’t been able to get a sample of this ransom Trojan until recently. The newly spotted details have revealed some specific traits of this infection. The strain relies on the ChaCha20 stream cipher to make data inaccessible. The encryption key is additionally encoded by an RSA-2048 public key for greater entropy.
Having encrypted a file, Mount Locker appends its name with a string in the following format: *.ReadManual.ID. The ID part is uniquely assigned to each victim and usually consists of eight random alphanumeric characters.
Interestingly, the harmful program makes a few changes to the system registry to make the ransom note pop up automatically whenever a victim tries to open an arbitrary encrypted file. The how-to document (RecoveryManual.html) includes tips on how to visit the Tor site, which is used to interact with the attackers via a built-in chat feature.
Mount Locker’s cryptography implementation appears to be flawless, which means that there is no way to defeat its encryption at this point. The only way to get files back without paying the ransom is to restore from a backup if any.